Disclaimer: Organizations are not required as a matter of law to comply with this document, unless legislation, or a direction given under legislation or by some other lawful authority, compels them to comply. This document does not override any obligations imposed by legislation or law. Furthermore, if this document conflicts with legislation or law, the latter takes precedence.
The Supreme Committee for Delivery & Legacy (SCDL) issued this cyber framework to set a benchmark for all involved in the FIFA World Cup to follow. The framework defines the core cyber-competencies and cyber-capabilities needed to safeguard critical national services that support the FIFA World Cup. Because there will be more digital presence than ever before, there are additional challenges with security and privacy. The Security Committee, with the help of numerous global partners, developed the Qatar Cybersecurity Framework (QCF) to ensure a safe and secure event.
The SCDL took a capability-based approach to define the framework that takes into consideration the risks identified by various entities. This approach focuses on embedding must-have capabilities to mitigate those heightened risks. To identify the specific capabilities required, the SCDL looked at basic operational activities divided into layers surrounding data that will apply to all systems (see the bottom of Figure 1). The framework ultimately identified 14 cybersecurity capabilities that are labelled under three pillars: Prevention, Detection, and Response (see Figure 2). The SCDL released the framework and deployment guide that can be found here.
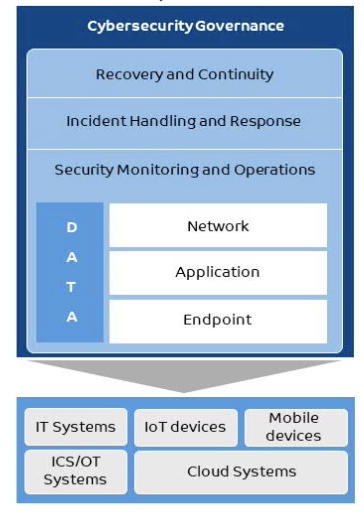
Figure 1
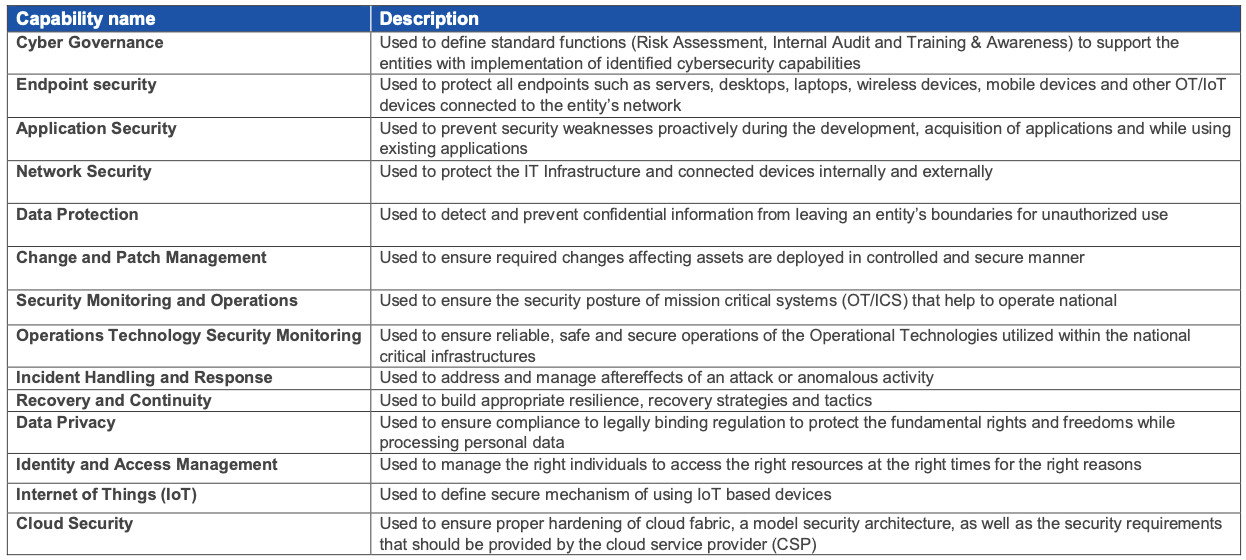
Figure 2
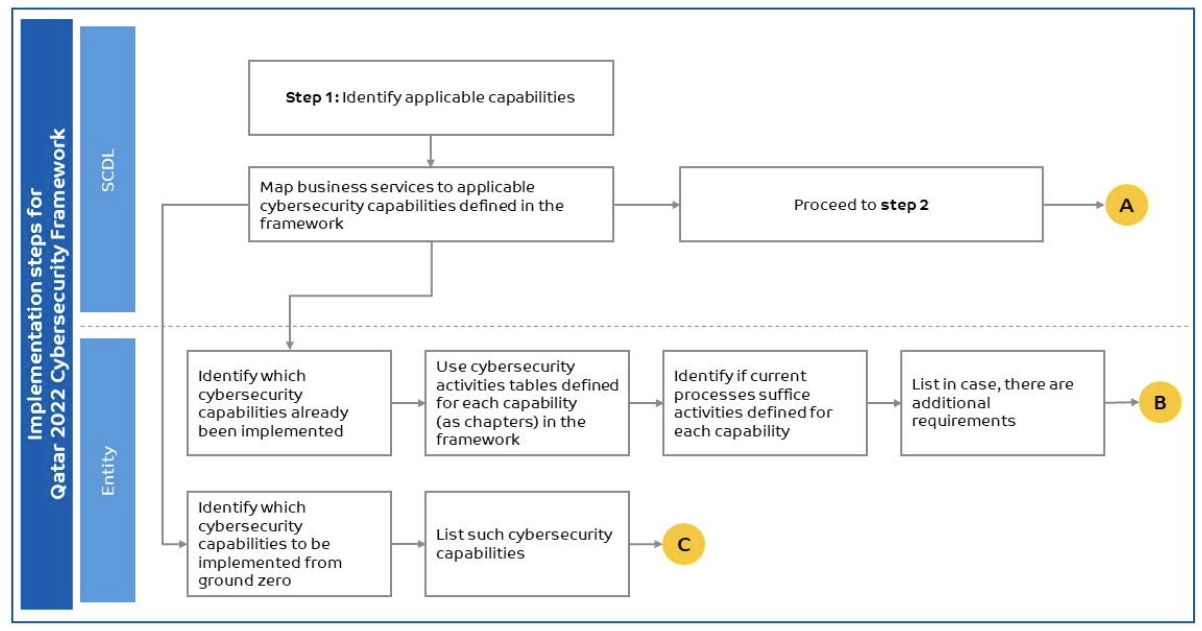
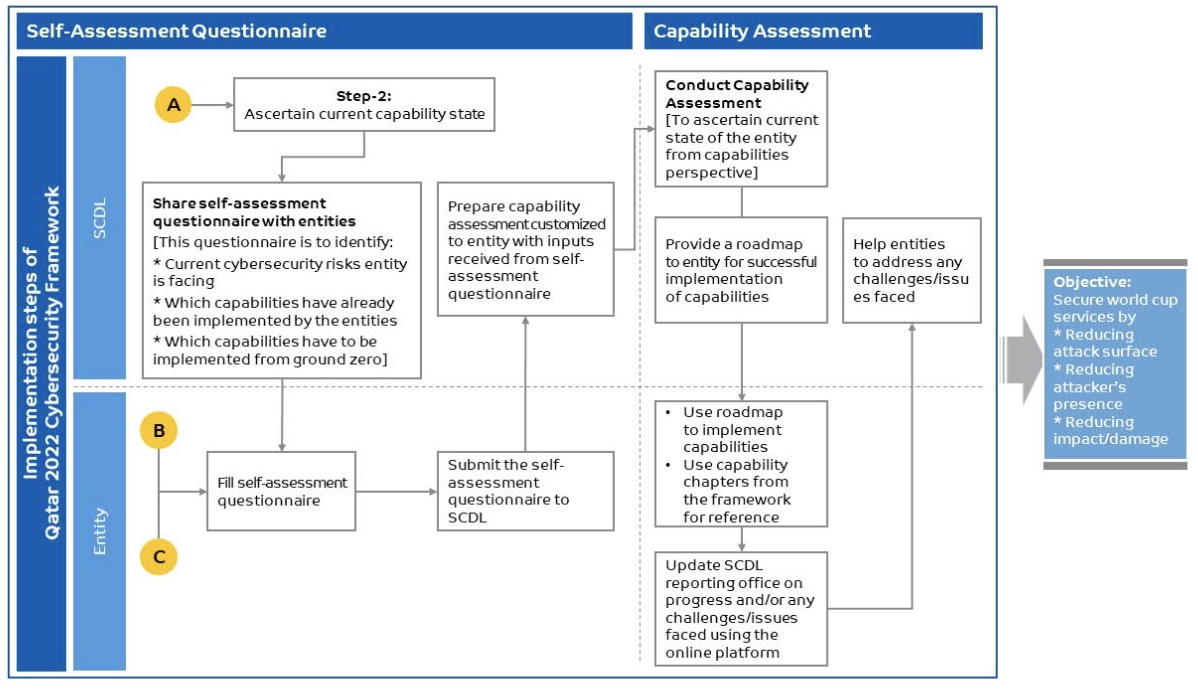
Implementation of the framework should follow a fairly simple process that the SCDL outlined which recommends the following:
-
Entities review the framework's cybersecurity capabilities and map the entity services to those capabilities.
-
Self-assess the implementation of those capabilities, and create a roadmap to address gaps in the implementation.
More details on the framework, the capabilities, and implementation can be found here.
The LogRhythm platform enables your organization to meet many QCF practices by collecting, managing, and analyzing log data. LogRhythm AI Engine (AIE) rules, alarms, reports, investigations, and general SIEM functionality also help your organization satisfy certain control practices outlined by the QCF.
LogRhythm understands that organizations may be at different points of compliance maturity, so the QCF module gives organizations the flexibility to realize value at any point along that maturity scale. The QCF module is focused on the control requirements traditionally used for best practice purposes. LogRhythm supports some QCF recommendations and decreases the cost of meeting others through pre-built content and functionality. Using advanced LogRhythm functionality such as NetMon, TrueIdentity, SysMon, Threat Research content, and Case Management may enhance pre-built content to better support an organization's compliance efforts.
IT environments consist of heterogeneous devices, systems, and applications—all reporting log data. Millions of individual log entries can be generated daily, if not hourly. The task of organizing this information can be overwhelming. Additional recommendations to analyze and report on log data render manual processes or homegrown remedies inadequate and cost-prohibitive for many organizations. LogRhythm delivers log collection, archiving, and recovery across the entire IT infrastructure and automates the first level of log analysis. Log data is categorized, identified, and normalized for easy analysis and reporting. LogRhythm’s powerful alerting capabilities automatically identify the most critical issues and notify relevant personnel. The QCF module and associated reporting package work out of the box with some level of customization available. Utilizing the QCF module assists in building and maintaining a sound compliance program
This document has the following given sections:
