AWS CloudTrail provides a management system that enables users to manage and deploy networks at geographically distributed locations. The System Monitor Agent can import CloudTrail events into LogRhythm for analysis. This document explains how to configure the collection of CloudTrail events using the web console's cloud to cloud functionality. This is available to LRCloud customers only.
Prerequisites
Before you start to configure collection from O365, you must ensure the following:
-
Customer is an LRCloud customer and has their environment hosted.
-
You have a valid AWS Access Key and Secret Access Key.
Initialize the Logs Source
-
Log into the web console as an Restricted Administrator User.
-
On the top navigation bar, click the Administration icon, and select Cloud Log Collection.
-
At the top of the page, click New Log Source.
-
Select the tile for AWS CloudTrail Events Sysmon Agent.
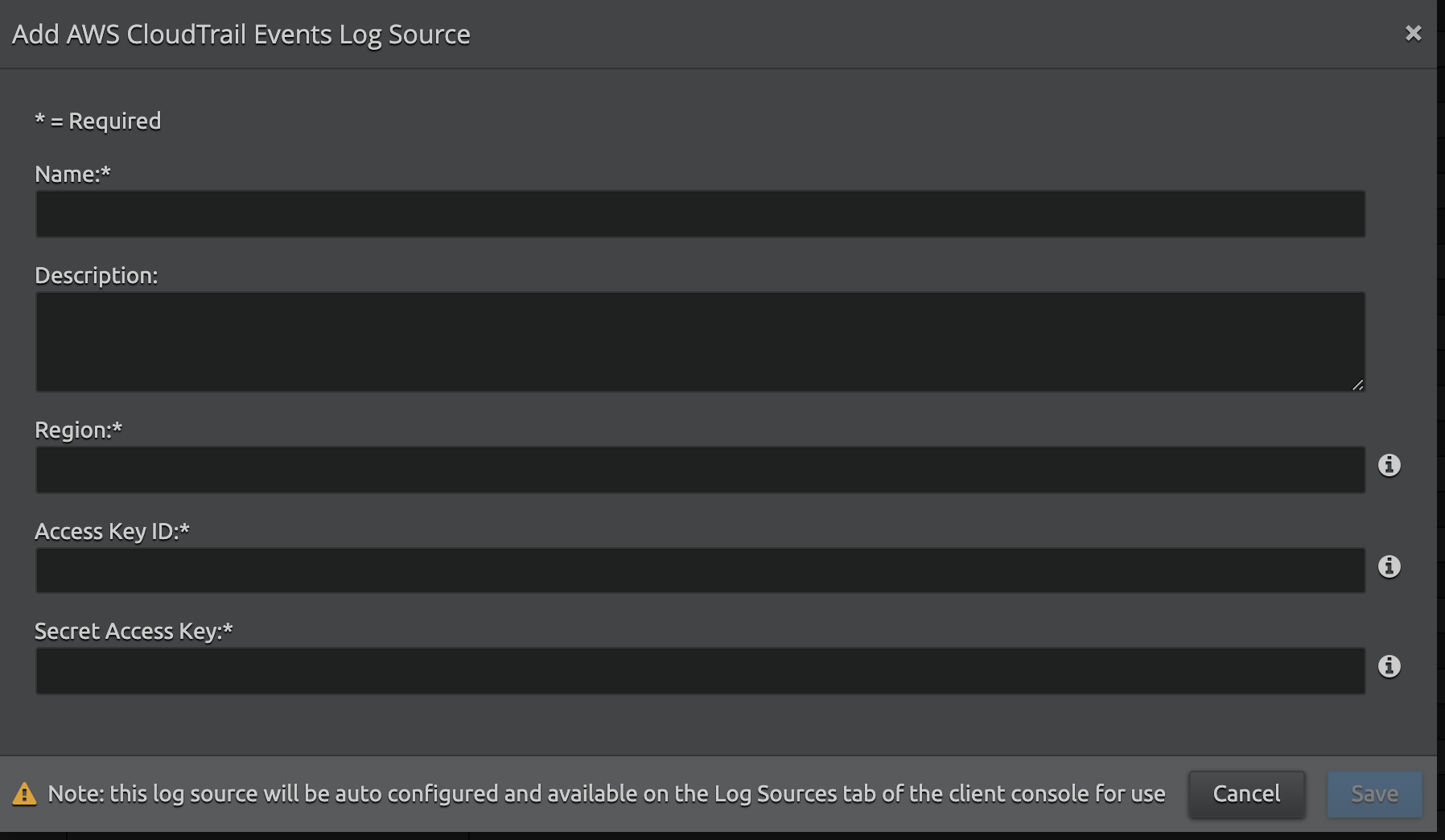
The Add AWS CloudTrail Events Log Source screen appears.
-
Enter the following details:
Setting
Description
Name
Enter the name for this log source.
Description
(Optional) Enter a description for this log source.
Region
Enter the endpoint region code for the specific AWS CloudTrail S3 bucket (for example, us-east-1). For more information, refer to CloudTrail Regions and Endpoints.
Access Key ID
Enter the AWS Access Key ID. for example, AKIAIOSFODNN7EXAMPLE
Secret Access Key
Enter the AWS Secret Access Key for example, wJalrXUtnFEMI/K7MDENG/bPxRfiCYEXAMPLEKEY
-
Click Save.
Using the information provided, a new active log source is created and accepted in the client console. Collection should start automatically within a couple of minutes.
The log source's host is the Platform Manager. However, it is recommended that a new host entity is created and the log source is moved to the new host.
For security purposes, the values entered are encrypted using LRCrypt.
Default Config Values for AWS CloudTrail Events Log Source
|
Setting |
Default Value |
|---|---|
|
APIPollingIntervalInMs |
5000 |
|
APIRetryCount |
3 |
|
MaxResultCount |
50 |
|
StartupDelayInSeconds |
30 seconds |
|
NumberOfBackDaysData |
1 day |
|
NumberOfBackMinutesData |
40 minutes |
|
BackOffTime |
15 minutes |
